Operation Bayonet
An international band of cyber police joined forces to bust the bosses of sinister darknet marketplaces
This account of an international crackdown on the internet’s darknet markets was adapted from the Darknet Diaries podcast created by Jack Rhysider.
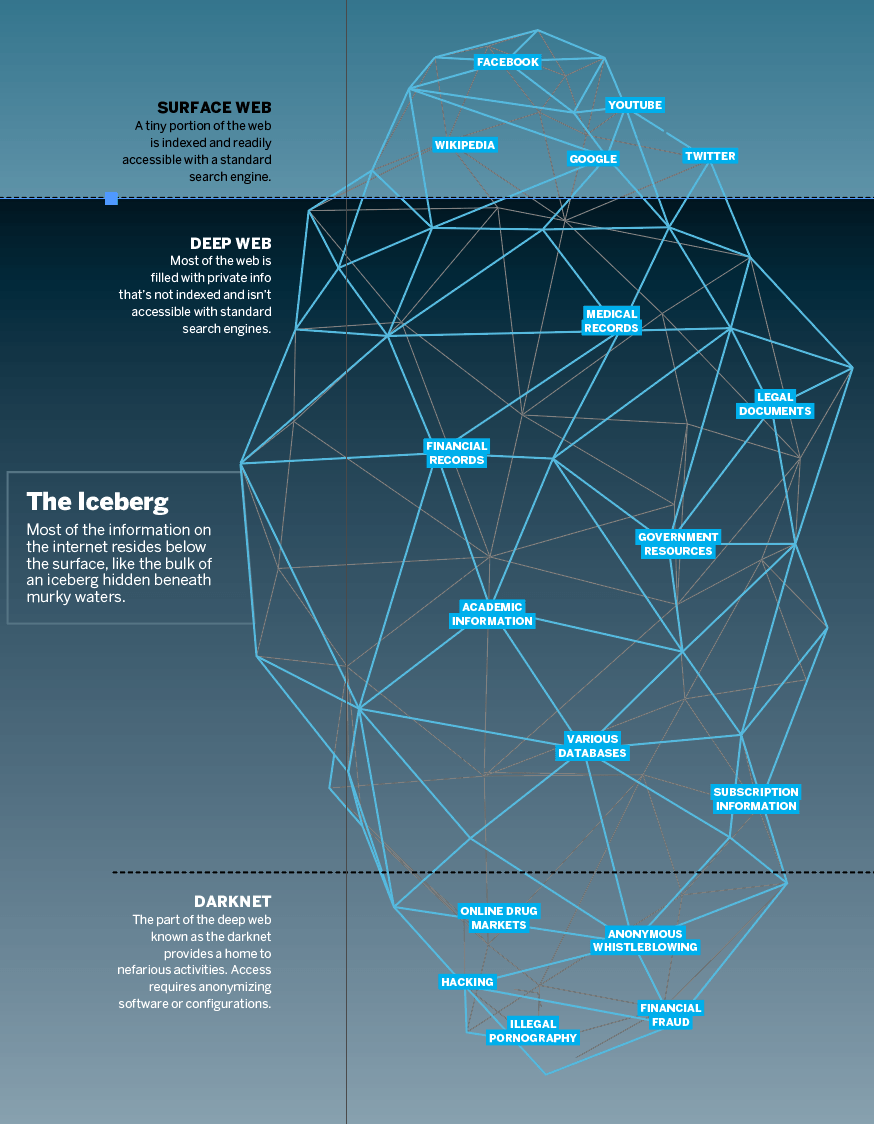
Some background on the darknet could foster a better understanding of the fate that befell a site called AlphaBay, one of the most popular darknet marketplaces ever.
Think of the darknet as a cloak of anonymity that hides users’ identities somewhere in the far reaches of the internet. Better yet, imagine walking into a nightclub where everyone’s required to wear a mask, white shirt, red tie and blue suit. That way, no one can tell the club patrons apart. It’s much the same on...
Technology
-
Retro Cool
By James Melton
|An upstart EV recalls a James Bond-like design equipped with a voice- activated cockpit -
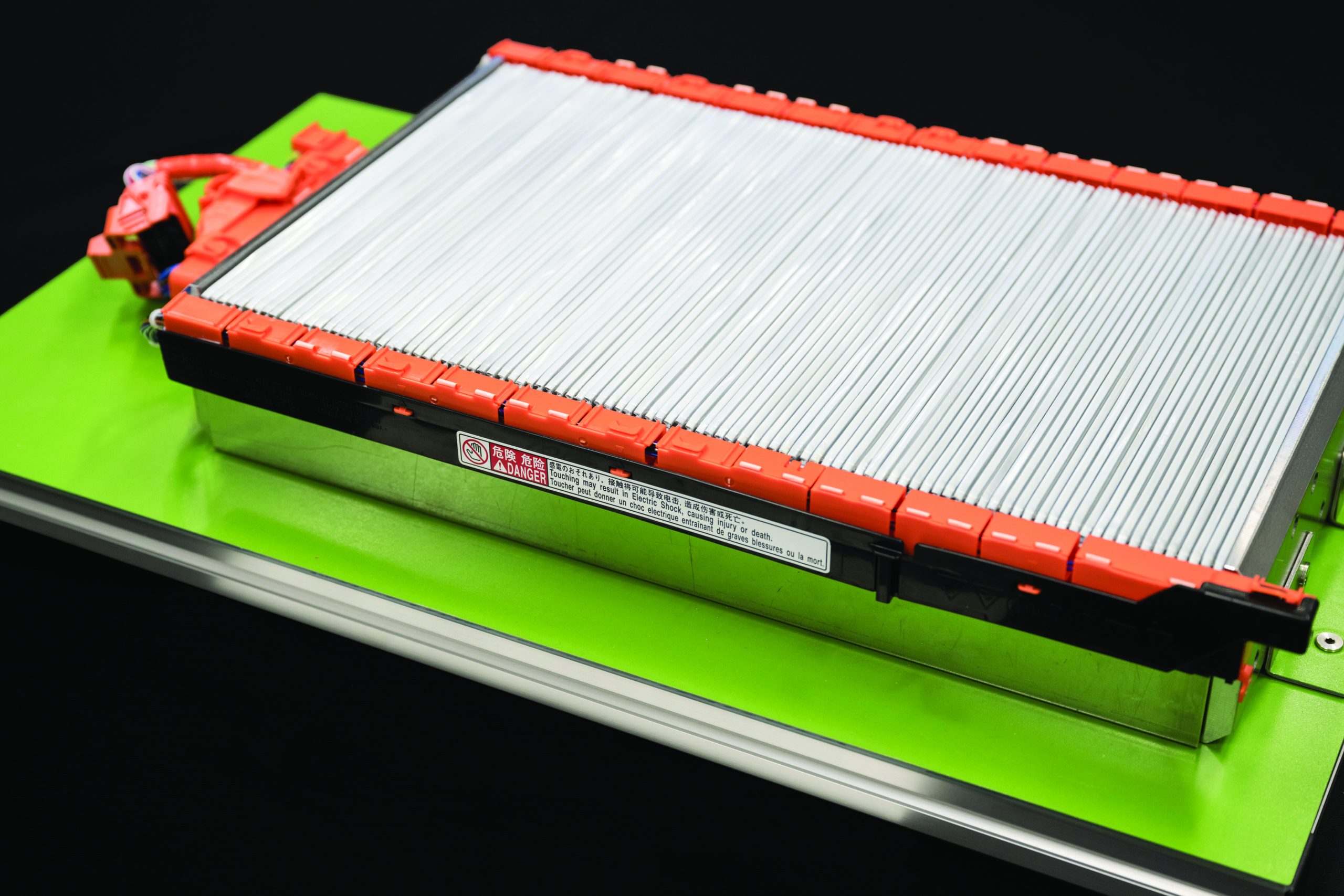
Fast-Charging Toyota
By James Melton
|The Japanese auto giant plans to jumpstart battery technology -
The Twelve Hottest New Cars of 2024
By James Melton
|From the practical to the aspirational, these new gas, hybrid and electric vehicles scorched their way to our shortlist -
4 of the Most Highly Anticipated IPOs in 2024
|The market for IPOs has been weak since the start of 2022, but there are several exciting companies expected to debut in 2024 -
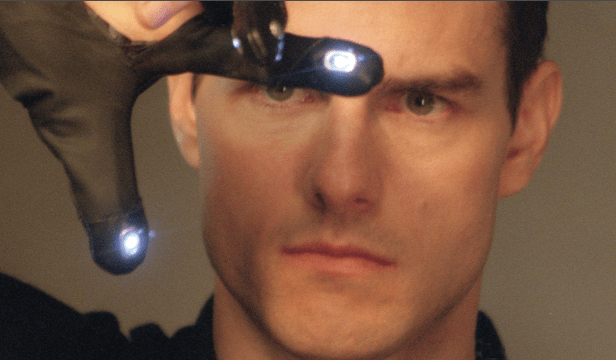
The Future of Policing has Arrived
By Ed McKinley
|Predictive analytics warn of criminal activity from the streets to the boardroom Computers are predicting when and where crimes will occur—but don’t expect a real-life remake of the 2002 sci-fi… -
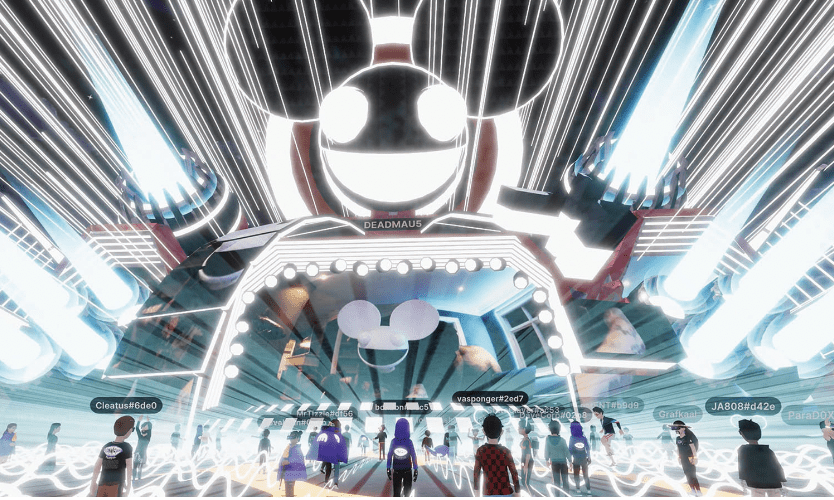
The Metaverse: Realities of Virtual Realities
By Mike Reddy
|Will the world look back upon the early days of the metaverse as a fit of delusion or the founding of an institution? Could virtual beer sales threaten real… -
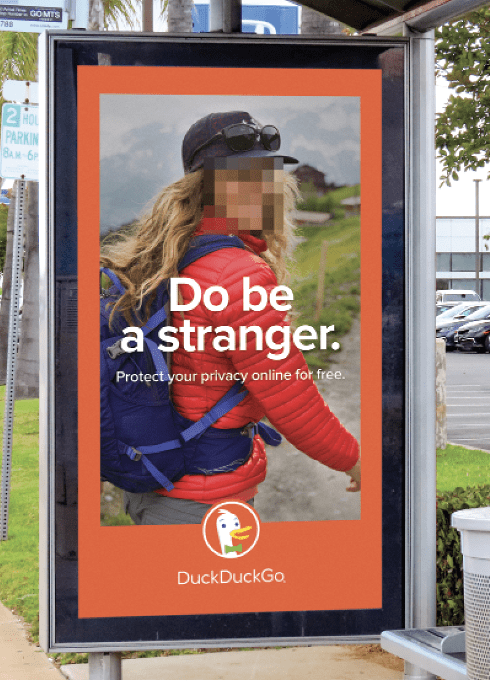
Duck Call
By Ed McKinley
|Despite a whimsical name, DuckDuckGo offers a serious privacy-oriented alternative to Google searches A google search for “luckbox” put a betting site at the top of the results and the… -
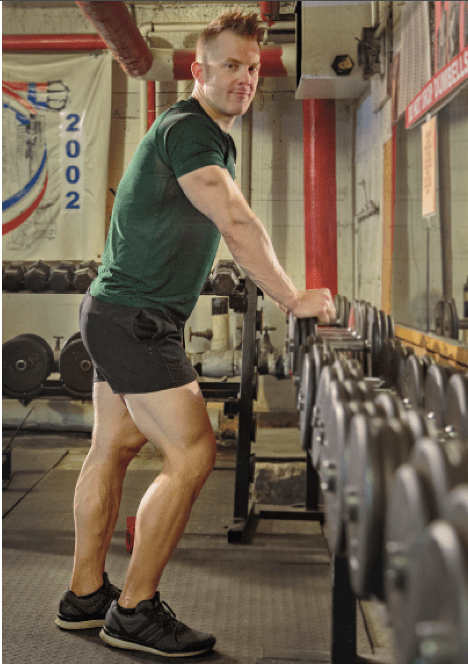
Losing the COVID 15
|A fitness expert offers advice on losing those pandemic-induced pounds Pre-COVID, you were cruising: Crushing personal records in the gym and keeping the physique lean and mean. But after a… -
Data Brokers the Menace of Surveillance Capitalism
|A secretive industry sells Americans’ data to marketers, companies and governments, both foreign and domestic. Is your privacy for sale? Data has become the world’s most coveted commodity—more valuable than… -
The Struggle to Protect data privacy
By Ed McKinley
|In 1890, future U.S. Supreme Court Justice Louis Brandeis was so alarmed by the new Kodak portable camera that he co-wrote a Harvard Law Review article entitled “The Right to… -
Data Privacy
By Ed McKinley
|Internet users casually offer up their valuable and sensitive personal data to any online entity that promises even a hint of convenience in exchange. Their carelessness is giving rise to… -
BIG TECH & THE LAW OF LARGE NUMBERS
By Tom Preston
|HOW EXACTLY DID BIG TECH GET TO BE SO … BIG? To paraphrase ben franklin, those who would give up essential privacy to purchase temporary convenience deserve neither privacy nor… -
Beneath the Deep Web: The Darknet
By Ed McKinley
|Everything evil proliferates in the mostly inaccessible outer reaches of the internet. Call it the darknet and don’t confuse it with the deep web. Popular search engines—such as Google, Bing… -
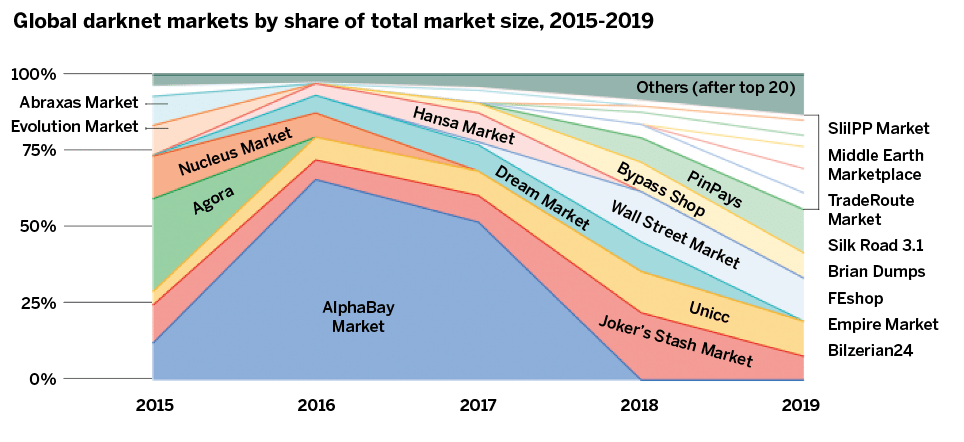
Darkest Markets
|The demise of the notorious Silk Road darknet market gave rise to even bigger and more nefarious online alternatives The FBI and Europol teamed up to shut down the Silk… -
Tracking the Darknet
By Luckbox
|Are the cops closing in on the criminals who run darknet marketplaces? Luckbox asks the contributors to this issue Law enforcement agencies are becoming better at tracking down darknet marketeers… -
Crypto Crime
By Luckbox
|Illicit marketplaces hidden in the darknet are anything but dead—in fact, they’re thriving Crypto crimes and online drug markets have disappeared from the headlines but haven’t disappeared from the darknet.… -
Why You Should Use The Onion Router
|The actionable aspects of the darknet begin with embracing its dominant browser Hardly anything’s all good or all bad, and the roundly criticized anegative side, the darknet’s anonymity provides shelter…